Cybersecurity is a critical and evolving field dedicated to protecting individuals, businesses, and governments from online threats. Amid transformative advancements such as AI, cloud adoption, quantum computing, and fluctuating geopolitical risks, organisations are navigating an increasingly complex cyber threat landscape.
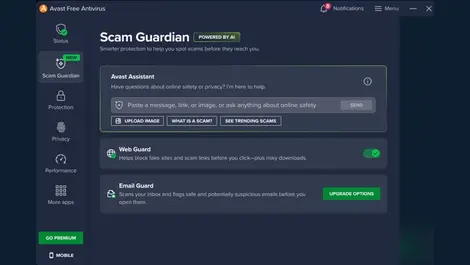
Recent developments across the cybersecurity sphere highlight crucial topics including ransomware surges, deepfake scams, API security lapses, identity management complexities, and the growing importance of Zero Trust frameworks. These trends underscore the need for proactive strategies, comprehensive threat detection, agile responses, and a strengthening of human and technological defenses.
With expanding attack surfaces driven by remote work, Internet of Things (IoT) devices, and digital transformation, there is a paramount focus on integrating AI-powered solutions, enhancing data protection, and addressing skills shortages. Initiatives promoting diversity, education, and collaborative partnerships continue to be essential in fortifying cyber resilience.
Exploring these themes through the latest stories and expert insights encourages readers to deepen their understanding of contemporary cybersecurity challenges and solutions, emphasizing actionable knowledge to help safeguard digital futures in an interconnected world.
 Brennan boosts sovereign SOC as demand shifts onshore
3 days ago
Brennan boosts sovereign SOC as demand shifts onshore
3 days ago
 Orro launches AI CTEM service for Australian firms
4 days ago
Orro launches AI CTEM service for Australian firms
4 days ago
 Adactin launches graduate programme to bridge IT skills gap
4 days ago
Adactin launches graduate programme to bridge IT skills gap
4 days ago
 Australian skincare founder hit by chargeback scams
4 days ago
Australian skincare founder hit by chargeback scams
4 days ago
 Australian firms warned on AI atop weak mobile systems
5 days ago
Australian firms warned on AI atop weak mobile systems
5 days ago
 Check Point launches Perth data residency SASE site
Last week
Check Point launches Perth data residency SASE site
Last week























































.webp)