The Ultimate Guide to Ransomware
A curated Australian edition of TechDay news, analysis, interviews, reviews, job moves, and related resources for Ransomware.
What to know about Ransomware
Ransomware represents a significant and evolving threat in the cybersecurity landscape, characterized by malicious software that encrypts data or locks systems until victims pay a ransom. It targets individuals, businesses, critical infrastructure, and government entities, often resulting in severe operational disruption and financial loss.
The stories under this tag explore the expanding scope of ransomware attacks—highlighting their increasing sophistication, the rise of ransomware-as-a-service models, and their impact across sectors like healthcare, manufacturing, finance, and public services. They also delve into emerging tactics such as data exfiltration for double extortion, targeted attacks on cloud and mobile platforms, and the role of artificial intelligence in both facilitating and combating these threats.
Readers will find insights into preventive measures, incident response strategies, and resilience-building through technological solutions such as advanced backup systems, cyber insurance, and threat intelligence collaborations. The content underscores the critical importance of continuous vigilance, employee training, and adopting layered defenses to manage ransomware risks effectively.
Engaging with these stories equips readers with up-to-date knowledge on ransomware trends, enabling individuals and organisations to better understand the threat dynamics and make informed decisions to protect their digital assets and maintain business continuity in an increasingly hostile cyber environment.
Australian Ransomware News
Regional stories with direct local relevance
The connectivity stack: Why Australian ICT leaders are rethinking where their websites live
Offshore web hosting is becoming harder to justify as Australian firms weigh latency, sovereignty and support risks across their digital stack.

Why Australian SMEs can't afford to treat cybersecurity as an afterthought
Rising attack volumes are exposing under-resourced SMEs to downtime, lost contracts and regulatory risk unless security is built in now.

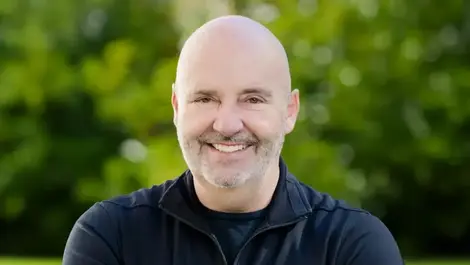
Aon appoints Quinton Kotze as Head of Cyber Solutions
Boards are under growing pressure to tackle ransomware and breaches as Aon expands its Australian cyber practice with a seasoned hire.

Cowbell appoints Gerry Power as general manager Australia
As cyber claims rise and broker demand grows, the insurer is deepening its Australian push with a newly created local leadership role.
.webp)
Australian budget boosts AI, but cyber gaps remain
Despite welcome AI funding, tech leaders say small firms still lack the cyber defences needed to adopt new tools safely.

Rapid7 launches Cyber GRC for tighter Australia rules
Australian businesses face sharper reporting deadlines as Rapid7 opens early access to software that ties compliance to live security risk.
Analyst Insights
Research and market analysis connected to Ransomware
TrendAI named Gartner endpoint leader for 21st time

Why your cybersecurity firm's Google rankings are a security risk in disguise

Group-IB named a Leader in Gartner cyberthreat report

Check Point tops Miercom hybrid mesh security benchmark

Check Point tops Miercom hybrid mesh security benchmark
Featured News
Expert Columns

Your Immune System Doesn't Wait. Neither Should Your Security
The connectivity stack: Why Australian ICT leaders are rethinking where their websites live

Why Australian SMEs can't afford to treat cybersecurity as an afterthought
A long time ago in a galaxy far, far away…Cybersecurity was already hard

The Death of the Firewall

Why 'strong passwords' can't save you from AI

One click can trigger a breach, but security can stop it

VPN vulnerabilities don't have to become breaches
Building security outcomes for small businesses: Why breaches persist despite available tools

Small alert, big defense: Inside a SOC's early-morning response
Interviews
Interviews and video coverage from the network
Everpure preparing for new era of cyber resiliency

Exclusive: Check Point warns SMEs on rising cyber risk

Exclusive: Cohesity's James Blake warns on rising ransomware risks

Exclusive: Cohesity explains why cyber resilience beats prevention

Exclusive: Veeam's Ben Young sounds alarm on backup risks in AI era
Recent Ransomware News

Australian firms urged to rethink ransomware defences
Ransomware is hitting Australian large businesses harder than global peers, with most victims still paying attackers despite backup defences.

Why your cybersecurity firm's Google rankings are a security risk in disguise
Enterprise buyers may never reach the sales call if a security firm is absent from search results, because digital authority now shapes trust and deal flow.

Experts warn passwords no longer sufficient in AI era
Australian firms are being urged to adopt passwordless logins as AI tools and data leakage make stolen credentials easier to exploit.
Semperis expands Purple Knight for government clouds
Agencies using Microsoft Government Community Cloud High can now scan cloud identities for weaknesses, closing a gap in hybrid security oversight.

CyberCX expands Collingwood cyber deal into major partnership
The expanded tie-up gives Collingwood extra protection for member and supporter data as cyber threats intensify across Australian sport.

Macquarie wins Netskope APJ managed services award
The deal underlines rising demand for bundled cloud security as Australian agencies and businesses face tighter compliance and AI-related data risks.

CMTG bets on backup as cyber resilience demand rises
Rising ransomware and outage costs are pushing businesses to treat backup as a board-level priority, boosting demand for recovery services.

World Backup Day warns firms on data recovery gaps
Many firms still fail recovery tests, leaving cyber attacks or outages able to halt services and expose critical data.

Australian firms urged to rethink backup amid cyber risk
Only 42% of Australian organisations back up all workloads, leaving many exposed when ransomware or hardware failures hit.

Infotrust buys Catalyst Cyber in AUD $5m federal push
Infotrust to acquire Canberra cyber firm Catalyst Cyber in an AUD $5m deal, fast-tracking access to high-assurance federal government work.

Survey finds Australians suffering cyber breach fatigue
Survey finds many Australians shrug off data breach warnings, seeing cyber attacks as inevitable despite rising risks and tailored support calls.

Australia warned over AI-fuelled surge in cyberwarfare
Australia faces AI-driven cyberwarfare “boiling point” as attacks surge, ransomware payouts soar and security remains dangerously reactive.

CyberCX becomes official cyber partner to AFL, AFLW
CyberCX signs two-year tie-up as Official Cyber Security Partner of the AFL and AFLW, covering league, clubs and Marvel Stadium's ARC system.

OpenText launches Secure Cloud for Australian MSPs
OpenText rolls out its revamped Secure Cloud in Australia, targeting MSPs with unified security, backup and local AUD $ billing tools.

Slipstream Cyber joins Atmos incident response panel
Slipstream Cyber joins Atmos' First Response and Remediation Panel to bolster early-stage digital forensics and incident response support.

Forensic IT names Chris Hatfield as Executive General Manager
Forensic IT has named Chris Hatfield executive general manager to lead digital forensics amid rising cyber incidents and governance scrutiny.

Reimagining healthcare IT from risk to resilience
Healthcare is at a digital crossroads, where resilient IT and observability define patient safety, clinical trust and sustainable care.

Infotrust sells Nexgen for AUD $50m to fund cyber push
Infotrust sells its Nexgen cloud and communications unit for AUD $50m to bankroll acquisitions and double down on sovereign cyber security.
Healthcare tops cyber attacks on Australian OT & IoT
Healthcare is now the prime target for OT and IoT cyber attacks in Australia, as security alerts per organisation surge to third globally.

Centacare boosts cyber resilience & halves Azure bill
Centacare overhauls disaster recovery with 11:11 Systems, boosting cyber resilience while slashing Azure data storage costs by half.
Job Moves

Aon appoints Quinton Kotze as Head of Cyber Solutions

Cowbell appoints Gerry Power as general manager Australia

Forensic IT names Chris Hatfield as Executive General Manager

OpSys appoints Shanna Daly as first Chief Security Officer
.webp)
Cybersecurity expert John Kindervag joins Illumio to drive adoption of Zero Trust Segmentation
.webp)